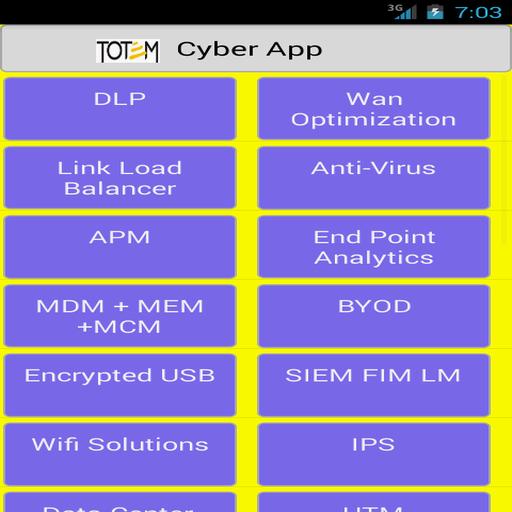

totem cyber security solutions
totem cyber security solutions
Enterprise Information Security is growing concern for the IT Managers, Business Process Owners and Customers. With the increase in the number of mobile users for business and personal activities, the risk of storing and managing the information securely for both corporate and personal data has become of greater importance.Each process established in an organization is a service asset and each such service asset is as critical as another for its streamlined operations.
We have leaped ahead of times when corporate security function used to dwell on physical security. Now our business is driven by both business ideas and technological advancements.Information Security in any corporate company boils down to the three fundamental concepts of IT security, they are, Confidentiality, Integrity and Availability. Now these concepts have to be applied while designing any process/procedure. But why? Is it so much essential? Yes it is. Yes it is. Below we present few new challenges in IT environments across industries and geographies to give the reader a perspective on the cyber security practices.
Challenges to IT environment
Application Security and Unencrypted traffic
Application security is gaining appetite for a growing number of threats on hacking into the application using the tools available on internet as well as through insider information. According to a study by security companies, nearly 86% of all websites had at least one serious vulnerability in 2012 and IT websites possess the most number of security issues with an average of 114 serious vulnerabilities per site. How do such bizarre numbers appear? Let’s take a Hotel Industry’s HMS (Hotel Management System) application for a quick analysis.
HMS is the central application to which all the other supporting functions and different unit’s applications are integrated. There is a constant communication back and forth between these unit’s and the central HMS application for various activities like registrations, purchase, orders, bookings, billings etc. This invariably makes the HMS application as the core source of information for the hackers.
However, the hackers have opted for variety of means to exploit the central HMS application. While most of security features are built on this central piece but the supporting features of the HMS tool are not configured for security during their development. These become the resting places for hackers for data.
The best way to prevent any kind of loss of information through the HMS portals and its supporting infrastructure is to review the applications and the infrastructure on the regular frequency for any presence of malware or malicious code and different kinds of vulnerabilities.
Vulnerable WiFi access
In a general WiFi or guest WiFi access area, the companies don’t reserve any restrictions on the security of the information being accessed by the customers using the WiFi setup. However, the hackers or customers with malicious intent or people on espionage, bank on the WiFi access area for breaching into the corporate network. There are a comprehending number of tools available in the internet for scanning footprints, reconnaissance, gathering the network topology and installing malware or performing any kind of man-in-the-middle attacks.
Steep increase in Malware
Antivirus industries have been incessantly monitoring the new malware being released in the internet and updating their software to mitigate the risks that arise from these malwares. However, keeping the company’s information systems up to date to defend against the new malicious code released in the internet is critical for safer environment.